
Maximize Productivity with Reliable IT Services & Support
NSN Management works as a strategic IT partner to your business, helping to eliminate IT complexity, maximize productivity, and help you better focus on the things that truly matter.
NSN Management works as a strategic IT partner to your business, helping to eliminate IT complexity, maximize productivity, and help you better focus on the things that truly matter.
When your business encounters an IT problem, productivity grinds to a halt. Even minor issues can disrupt critical workflows, divert attention from important projects, and add stress to your day. Have you struggled with any of these issues?
Network technology that stops working, even just for a few hours, harms team morale and slows productivity. When you’re facing chronic IT problems, it can cripple your business.
If you’ve ever lost valuable data, you know how devastating it can be. When you operate without a customized data backup and recovery system, you’re exposing yourself to great risk.
Are you sure you’re spending your IT budget in the right way? Most small and midsized companies struggle to define a clear roadmap for business-technology alignment.
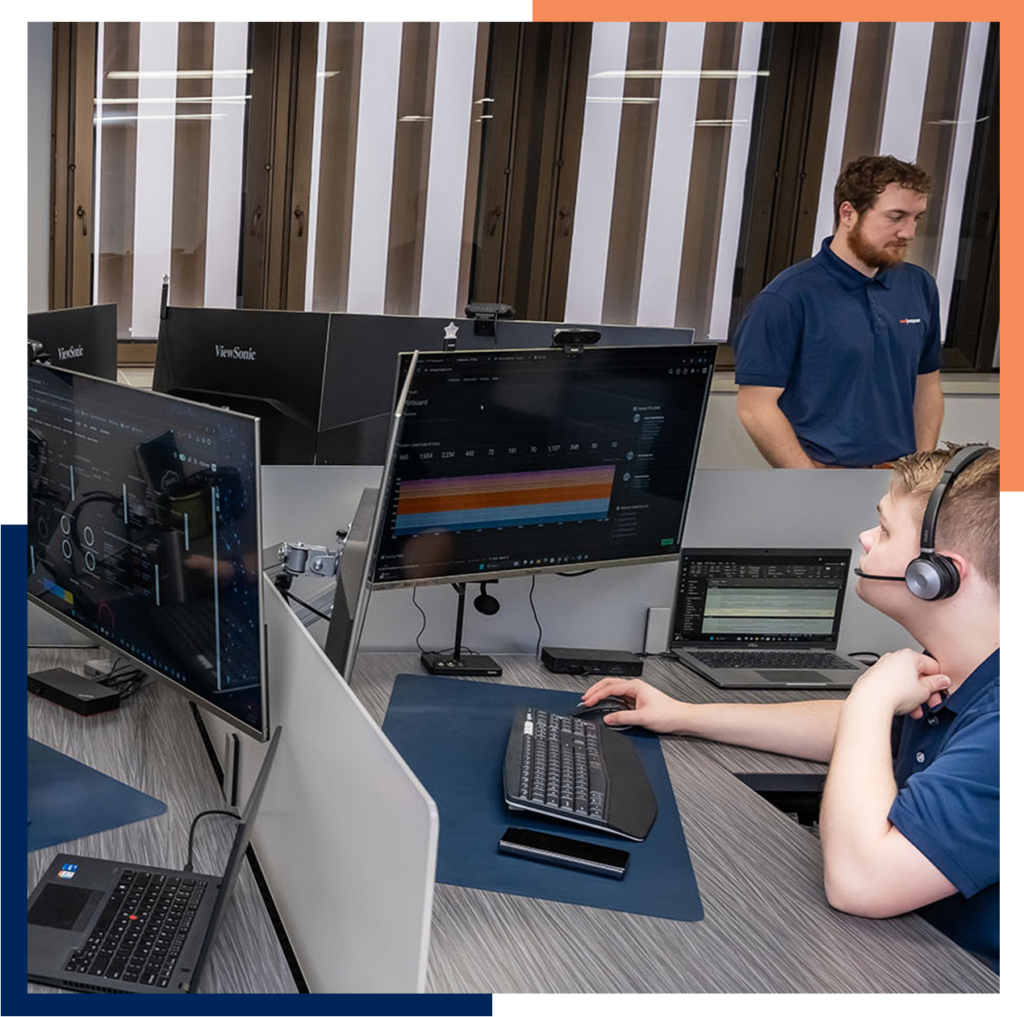
Having NSN Management as your IT services partner puts you on a fast track to technology confidence. We’ll analyze your network, develop a clear strategy for technology success, and work side-by-side with your team to maximize productivity.

The guiding principle for NSN Management is that client satisfaction comes first. We simply wouldn’t exist as a company unless our clients were consistently happy with our service. Here’s how we ensure that you stay thrilled with our work, long after you bring us onboard.
Technology now plays a huge role in the success of businesses in Oklahoma. To thrive in this fast-evolving IT landscape, you don’t need just an IT services firm; you need a trustworthy partner who you can count on for expert advice and fast and friendly IT support.
You’ll always have someone at NSN Management to talk with about your IT problem. Friendly support in plain English (no techspeak) that always makes you feel listened to and valued.
We hire technicians with top credentials then we train them on our technology support culture and methods. The result is the support you need to get back to work, delivered as efficiently as possible.
Flat-rate support from NSN Management gives you unlimited access to remote and onsite support. All your IT problems get handled, and your IT support bill never changes from month to month. We’ve earned near-perfect 5-star reviews from our clients!
Comprehensive, 24/7 network technology support for all your devices, from servers and PCs to printers and mobile devices.
Support for your in-house IT team that fills skill gaps, improves service quality, and provides targeted expertise for major projects.
Vigilant security monitoring to quickly respond to cyber threats and focus your security budget on what matters most.
Next-generation business telephone systems that help you reach new levels of productivity, collaboration, and cost efficiency.
Full-service Microsoft 365 and Azure consulting, enabling a smooth and secure transition to Microsoft’s latest productivity software.
Empower your staff to securely share data and collaborate with replacing costly infrastructure with cost-effective cloud solutions.
We’re deeply committed to helping Oklahoma’s business community thrive. From our two offices, we provide responsive IT service expertise across the state.
We’re proud to serve Oklahoma City’s diverse and thriving business community.
Our Process is streamlined with efficiency every step of the way

Phew! We made it! The first 30 days is in the books and you are well on your way to a better IT experience! Over the next 3 months, you will have regular check-ins with your IT team and will be presented with your 3-year technology roadmap.

Through partnership with NSN Management, we'll guide you to make the best decisions for your individual business needs. We pride ourselves at being the best and ensuring our customers needs are met.
Get Started today and we can work together to finding a solution for you.